- Platform Use Cases
-
Outside-In Scanning
Outside-In Scanning
-
Cooperations
Cooperations
- Services
With nothing more than a company's domain, cysmo® generates a detailed report on its externally visible digital weaknesses in real time (<1 minute).
Portfolio View
Portfolio analysis at the touch of a button in real time
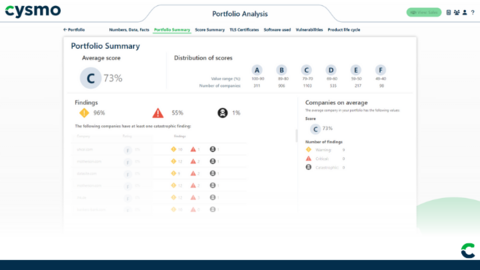
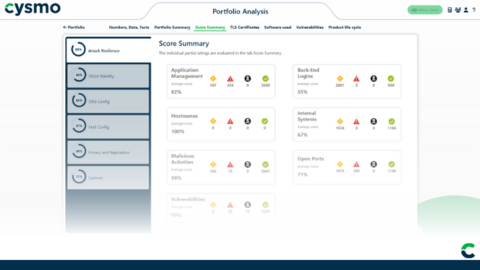
cysmo® analyzes the entire portfolio at the click of a button: In order to maintain an overview of even larger portfolios, we have created the Portfolio Analysis feature, which allows you to analyze the entire portfolio at the touch of a button.
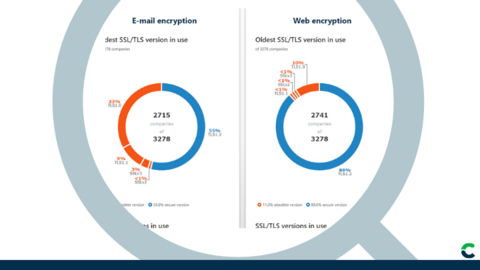
This allows you to gain an overview of the accumulation risk and display it according to various areas, e.g. according to criteria such as "software used", "use of cloud infrastructures" or "server locations".
With the Portfolio View from cysmo® you always have control and an overview of your entire insurance portfolio.
Use our advanced features to identify risks precisely, manage them effectively and react proactively to change:
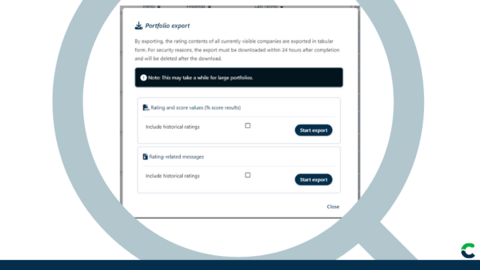
- Use detailed data with the help of various export functions (.csv, .xlsx)
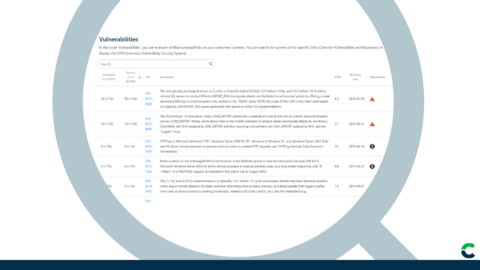
- Überprüfen Sie die eingesetzte Software innerhalb des Portfolios bei neuen bzw. Zero-Day-Schwachstellen effizient
- Use the option of mass uploads of portfolios
- Make risk management visible in the form of changes in the portfolio using the monitoring and alerting tool.
- Be informed when changes occur in your portfolio or send the notification directly to your customer.
cysmo® not only offers you the opportunity to uncover risks, but also to use this information in a targeted manner to inform and protect your customers in the best possible way.
Start now and transform your risk management with cysmo® to take security and efficiency to a new level!
Optimize your cyber risk assessment with cysmo®
Book your demo now!
Experience the power of cysmo® with a personal demo. Choose a date that suits you to get an exclusive introduction to our cysmo® platform. Our team will show you how you can optimize your risk analysis and decision-making processes.
Curious?
Financial companies have the exclusive opportunity to gain insight into the next generation of risk analysis through our free report to gain insight into the next generation of risk analysis.
Outside-In-Scanning Software
cysmo® Plattform
Angebot anfordern