-
Platform Use Cases
Platform Use Cases
- Platform Use Cases
-
Insurer & Broker
Insurer & Broker
-
Companies and Supply-Chains
Companies and Supply-Chains
- M&A, PE & Banks
-
Outside-In Scanning
Outside-In Scanning
-
Cooperations
Cooperations
- Services
- Free Guide _ cam1_eu
- Demo _ cam1_eu
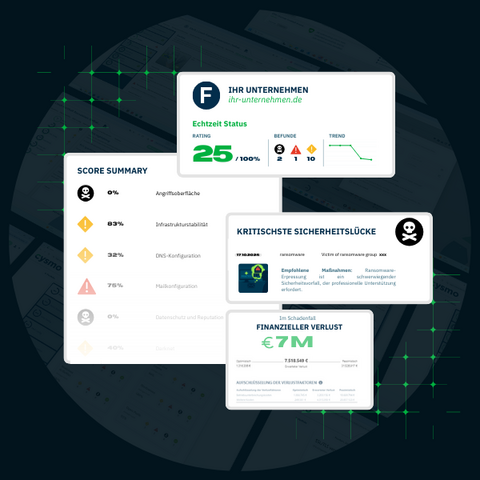
Track Cyber & Supply-Chain Risks in Real Time
Your company is digital.
Unfortunately, so is your risk.
With cysmo® — the German innovation technology — you can see within 60 seconds — in real time — which cyber risks from the outside affect your business — including digital dependencies you may not even know about.
AWARD WINNER 2026!!! cysmo® is Winner of the “Cyber Security Solution Provider of the Year 2026” Award Europe.
If IT fails, your business fails.
Cyber incidents don’t hit systems
they hit your business — revenue, production & service.
Today’s business is digital — every process depends on IT. A cyber incident isn’t just a “server down” event, it means:
- Orders stop
- Production halts
- Customers can’t buy
- Reputation suffers
- Fines & liability hit management
Cyber risk is no longer optional governance. From Europe (NIS2, DORA) to the United States (SEC, NYDFS) and Latin America (LGPD and regional data protection laws) — management is legally accountable for digital resilience and third-party risk oversight.
Cybersecurity is no longer a technical topic.
It’s corporate governance.
Your company | What attackers see — you must see first.
Do you know your external attack surface? It determines your vulnerability.
Companies invest heavily in internal security — important!
But what really matters is how visible you are from the outside.
That’s exactly where attackers begin.
Your shop looks modern → but your server version tells a different story.
Your IT service provider has a vulnerability → and you pay the price.
An employee uses corporate logins on a public site → that password is already circulating on the darknet.
Your website calls a service → that you’ve never discussed.
A default login is open → because the project had to finish quickly.
Management needs the external perspective,
because that’s where your real risks become visible.
Your supply chain | 70 % of attacks start with others — not you.
Your most dangerous IT risk isn’t inside your building — it’s in your supply chain.
You invest in your own security. But what about your suppliers? Your agencies? Your hosting provider? Your SaaS tools? Your sub-suppliers?
All these external parties impact your business every day — and that’s where the most serious incidents occur:
A cloud service has an update issue → your shop is offline for hours.
An agency uses outdated software → your CMS gets compromised.
A SaaS tool is attacked → your customer data ends up on the internet.
An IT service provider has a vulnerability → attackers use their access to get to you.
You’re legally responsible — even when the fault lies with someone else.
That’s the trending reality under regulations around the globe.
cysmo® strengthens your IT — instead of replacing it.
Your team no longer has to find the needle in the haystack — you see immediately what truly matters.
Transparency doesn’t have to be complicated. But it does have to work.
One Domain. 60 Seconds.
Many cyber solutions start with complexity and results on old data(bases).
cysmo® is the opposite:
- realtime scans
- no installation, no system access required, no risk
- results in under 60 seconds
- instantly understandable — even for non-technical users
- continous monitoring
- alertings
- available in more than 10 languages
No technology discussion. No preparation.
Just clarity.
![[[Translate to "English"]] Allianz x cysmo](/fileadmin/public/Redaktion/Bilder/Logos/Customer/Allianz_x_cysmo.jpg)